As usual, the first step is to run a scan; I'm using nmap.
Output
We have 2 services:
80 http nginx: A web server.22 ssh: A classic SSH login.
Let's examine the website. When we try to navigate to the website using the IP, we receive a redirect to the domain silentium.htb. We need to edit our /etc/hosts file.
YOUR_IP silentium.htb
Now that we have access to the website, we can explore a bit. There are no emails, links, or inputs; it is simply a static website. Let's enumerate subdomains.
Output
Subdomain Exploration
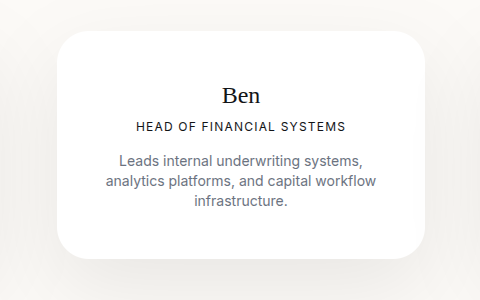
We found a subdomain staging. It's a Flowise service. We have the login page, but so far we haven't found any valid credentialss. Looking more closely at the static website, we can see at the bottom of the page the section contact. We identify the user as Ben. Let's try this one.
Using this vulnerability (CVE-2025-58434). Let's try to reset the password for Ben.
The first exploit
Output
The initial exploit was successful. Next, now reset the password of ben.
Save the tmp token in my case: GDHxpb6l1mPtggtVxk8sWexa8gu0SAki1pqpdtQ4KHSTF2eNOuoKQBcu3v6gKDSG
Let's continue to follow the PoC.
Output
We successfully changed the password.
Get the user access
Now that we have access to Flowise we have to find a way to gain user-level access. We can use this CVE-2025-59528 and use this script.
Running (with your credential)
Make sure you are running the netcat listener.
Now we have a console but we're inside a Docker container we must either find a way to escape the container or find a password and hope that ben reused one of them (this is very typical for this type of machine). Let's print the
env.
Okay we see two passwords r04D!!_R4ge and F1l3_d0ck3r, let's try to login to ben with one of the two. and we the r04D!!_R4ge we are in
Second part
Now we have to find a way to perform privilege escalation.
On port 3001,
Output
We can attempt to register, forge session cookies, and edit the database. Once we are registered on the service, we can leverage CVE-2025-8110. This results in root access.